A self-hosted VPN on a no-KYC VPS in a privacy-friendly country is one of the most cost-effective privacy upgrades you can make in 2026. For under $10 per month you replace a commercial VPN provider — whose logging policy you have to take on faith — with a setup where the trust boundary is your own. The two protocols worth running today are WireGuard and OpenVPN. They look interchangeable from a marketing page; they are not. This guide walks the real differences, the setup gotchas that matter, and the operational hygiene that keeps the box useful for years.
Why self-host instead of using a commercial VPN?
Trust boundary moves to you
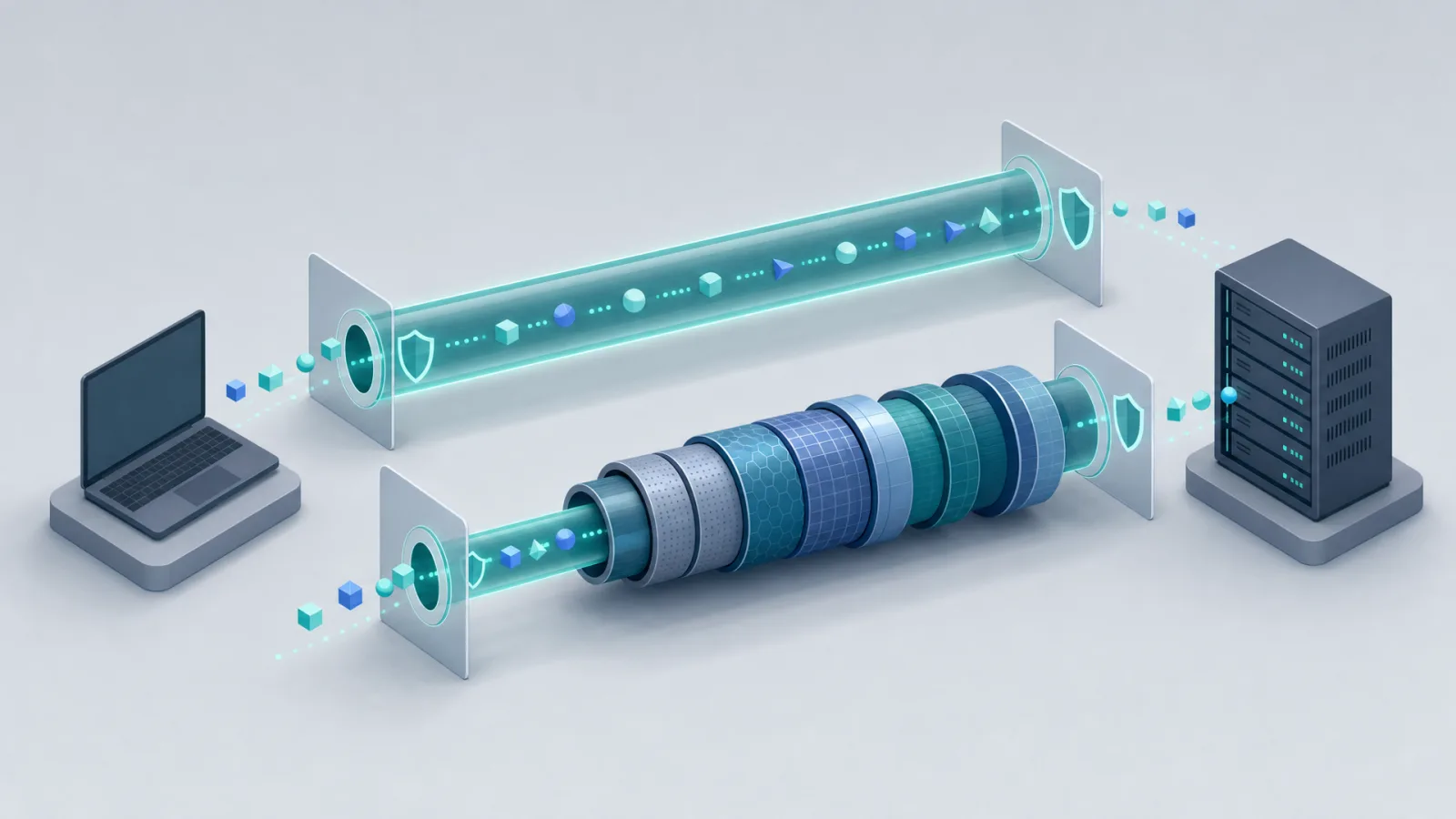
A commercial VPN provider sees every site you visit. Their privacy policy is a promise — auditable in only the loosest sense, even with public no-logs audits. When you self-host, the only entity that sees your traffic at the VPN layer is you. The host knows the IP exists and that traffic flows; what's inside the tunnel is opaque to them.
No KYC, no shared exit IP reputation
Commercial VPN exit IPs are continuously block-listed. As of 2026 most major providers' IP ranges are flagged by Cloudflare, Google captchas, financial-services anti-fraud systems, and streaming geofences. A self-hosted endpoint on a fresh datacenter IP with no history rarely hits any of those — until you abuse it, at which point the IP becomes burned and you spin up a new one.
Cost
Commercial VPN: $5–$13 per month per user. Self-hosted on a 1GB / 1 vCPU VPS: $5–$8 per month, supporting an entire household and easily hitting 200 Mbps on WireGuard. The crossover is at one user.
What you give up
Multi-country exit selection. A commercial VPN gives you 50+ exit countries with one click; self-hosting gives you exactly the country your VPS is in. The fix is to spin up two or three boxes in different jurisdictions — still cheaper than commercial.
WireGuard vs OpenVPN: protocol-level comparison
WireGuard at a glance
WireGuard is a modern VPN protocol designed by Jason Donenfeld, mainlined into the Linux kernel in March 2020. Code base: about 4,000 lines of C (versus ~70,000 for OpenVPN). Runs in kernel space on Linux, which is most of the speed advantage. Cryptography is fixed: ChaCha20-Poly1305 for symmetric, Curve25519 for key exchange, BLAKE2s for hashing, no algorithm negotiation. Configuration is a 4-to-10-line text file.
OpenVPN at a glance
OpenVPN is the established standard, in production since 2001. Runs in user space, uses OpenSSL or mbedTLS for crypto, supports a wide range of ciphers and authentication methods, and is configurable to a fault. Native support for TCP transport (essential for some restricted networks where UDP is blocked), TLS-based client auth via certs, and PAM/RADIUS pluggable auth. Mature tooling, easy to script, easy to audit, well-documented operational gotchas.
Side-by-side
| Dimension | WireGuard | OpenVPN |
|---|---|---|
| Code size | ~4,000 lines | ~70,000 lines + OpenSSL |
| Throughput on 1 Gbps link | ~95% line rate (~940 Mbps) | ~50–70% line rate (500–700 Mbps) |
| Handshake time | ~1 RTT | ~6 RTTs |
| Default UDP port | 51820 | 1194 |
| TCP fallback | No (use udp2raw or wstunnel) | Yes, native |
| Crypto agility | None (fixed suite) | Full |
| Mobile battery impact | Low (kernel + roaming-friendly) | Moderate |
| Obfuscation | External (udp2raw, awg) | obfsproxy, stunnel, tls-crypt-v2 |
| Audit surface | Small, formally verified | Large, well-reviewed |
| Operational maturity | Strong since 2021 | Strong since ~2008 |
The throughput numbers, explained
On a $10 VPS with a single vCPU and a 1 Gbps shared link, WireGuard will saturate the link until you hit the host's bandwidth shaper or the CPU bottleneck of the userspace network stack — typically 800–940 Mbps in 2026. OpenVPN on the same hardware will plateau around 500–650 Mbps because of TLS overhead and the userspace context-switch cost. For a household streaming 4K, both are plenty. For a dev pulling multi-gigabyte container images over the tunnel, WireGuard saves real time.
When OpenVPN is still the right choice
Restricted networks that block UDP
Hotel, university and corporate networks that drop UDP traffic break WireGuard cleanly. OpenVPN over TCP/443 looks indistinguishable from HTTPS at L4 and gets through. WireGuard can be tunnelled over TCP using udp2raw or wstunnel, but that's a second moving part and undoes some of WireGuard's simplicity.
Heavy obfuscation needs
If you need protection from active probing in a country with deep-packet-inspection-based VPN blocking — China's Great Firewall, Iran, Russia's recent enforcement against major VPN protocols — OpenVPN with stunnel or obfs4 has a longer track record. WireGuard's solution (AmneziaWG being the most actively-developed obfuscated fork) works but the ecosystem is younger.
Granular per-user authentication
If you're running a VPN for a small team and need to revoke individuals, OpenVPN's PKI model (each user gets a cert, revocation via CRL) is more ergonomic than WireGuard's "edit the config and reload" approach.
When WireGuard is the right choice
For nearly everything else: personal VPN, household VPN, mobile VPN with frequent network switching, performance-sensitive tunnels, low-power devices, and any setup where simplicity reduces operational risk. The 4-line config means the surface area for misconfiguration is tiny — a common cause of OpenVPN privacy leaks is people leaving compression on (CRIME) or using outdated ciphers because the config is intimidating.
Mobile clients
WireGuard's roaming behaviour — silently re-establishing the tunnel when the underlying network changes — is dramatically smoother than OpenVPN's, where reconnects often interrupt apps. On mobile, the battery impact difference is also real: WireGuard's kernel-level efficiency saves measurable percentage points of daily battery on a phone with always-on VPN.
Setup gotchas that bite people
MTU clamping
Both protocols add overhead to every packet (about 60 bytes for WireGuard, more for OpenVPN). If the underlying network's MTU is 1500 and the inner MTU stays at 1500, large packets get fragmented or dropped — the symptom is "small things work, large transfers stall." Fix on the VPS server: iptables -t mangle -A FORWARD -p tcp --tcp-flags SYN,RST SYN -j TCPMSS --clamp-mss-to-pmtu. WireGuard is somewhat self-tuning but TCP-over-UDP-over-TCP scenarios can still bite.
Port-25 abuse and the spam reputation problem
Most reputable hosts block outbound TCP/25 (SMTP) by default — without it, a compromised VPS becomes a spam relay within hours. As of 2026, virtually every offshore VPS provider blocks port 25 on shared IPs. Don't try to argue around it; if you genuinely need SMTP, request a static reputation IP and accept the longer onboarding. Run your VPN endpoint on the default IP and your mail server somewhere else.
ASN reputation
Datacenter ASNs get progressively more captcha pressure from Cloudflare, Google and most anti-fraud systems. Boutique offshore datacenter ASNs (small/mid-size IP ranges in Iceland, Moldova, Panama) often have cleaner reputation than the giant consumer-cloud ASNs. Pick the host accordingly. For more on this, see the VPN hosting use case.
Killswitch — PostUp/PostDown
A killswitch ensures that if the VPN tunnel drops, the device stops sending traffic instead of leaking around it. WireGuard implements this neatly with PostUp/PreDown hooks in the config — the canonical pattern is PostUp = iptables -I OUTPUT ! -o %i -m mark ! --mark $(wg show %i fwmark) -m addrtype ! --dst-type LOCAL -j REJECT. OpenVPN equivalent is the --route-up and --down-pre scripts. Test the killswitch by manually killing the VPN process and watching whether traffic still flows; if it does, the killswitch isn't engaged.
DNS leaks
Both protocols carry IP traffic; neither automatically routes DNS through the tunnel. Configure the VPN client to push a DNS server reachable only over the tunnel (often your VPS itself running unbound or dnscrypt-proxy). On Linux, install resolvconf integration or use systemd-resolved with the right scope. Test with dnsleaktest.com after every major OS or client update.
IPv6 leaks
If your client has IPv6 and the VPN only carries IPv4, IPv6 traffic bypasses the tunnel and exposes your real IP. Either disable IPv6 at the device level, or extend the VPN config to handle IPv6 inside the tunnel. WireGuard supports dual-stack tunnels cleanly; OpenVPN does too with the right server config.
Picking the right VPS for the job
For a personal or household self-hosted VPN, the spec floor is low: 1 GB RAM, 1 vCPU, 20 GB disk, and the network capacity to match the tunnel speed you want. WireGuard barely uses CPU; OpenVPN benefits from one extra core if you're pushing 500+ Mbps. Pick the country first using the jurisdiction guide, then size the box. Browse VPS plans for entry-level options under $10 per month in seven jurisdictions, and read the VPN hosting use case for setup-specific notes.
Operational hygiene
- Rotate the box every 6 to 12 months. Datacenter IPs accumulate baggage. A fresh VPS with a fresh IP costs $9 and takes 10 minutes — cheaper than fighting captchas.
- Disable password SSH. Key-only, fail2ban or sshguard, optionally a non-22 port to cut log noise.
- Run unattended-upgrades. A VPN host that's a year behind on kernel patches is more dangerous than no VPN.
- Monitor traffic, not contents. A simple
vnstatinstall tells you when something's off — sudden uplink saturation usually means the box is being abused. - Pay in crypto, no KYC at signup. The crypto payments guide covers what the host learns about you per coin choice.